In 2024, Google recorded 75 zero-day vulnerabilities actively exploited in the wild, down from 98 cases in 2023 but still significantly higher than 63 cases in 2022. Within the crypto market alone, the North Korean Lazarus Group stole $1.34B across 47 attacks in 2024, an increase of 102% year over year. In February 2025, the $1.5B Bybit hack shattered all previous records.
It is clear that zero-day attacks are no longer a distant concept. They occur daily and directly impact user assets. This article explains what a zero-day attack is, how it works, the largest losses in crypto history, and most importantly, how to reduce risk.
What is a Zero Day Attack?
A zero-day attack is a type of cyberattack that exploits a vulnerability in software or systems before the development team becomes aware of its existence. The term “zero-day” means that when attackers discover and exploit the vulnerability, developers effectively have zero days to prepare or deploy a fix. The attack happens before any defensive measures are in place.
In crypto, zero-day attacks can target many layers of infrastructure, including wallets, exchanges, smart contracts, compilers, web browsers, mobile operating systems, and even blockchain consensus mechanisms. Anywhere software operates, the risk of a zero-day vulnerability exists.
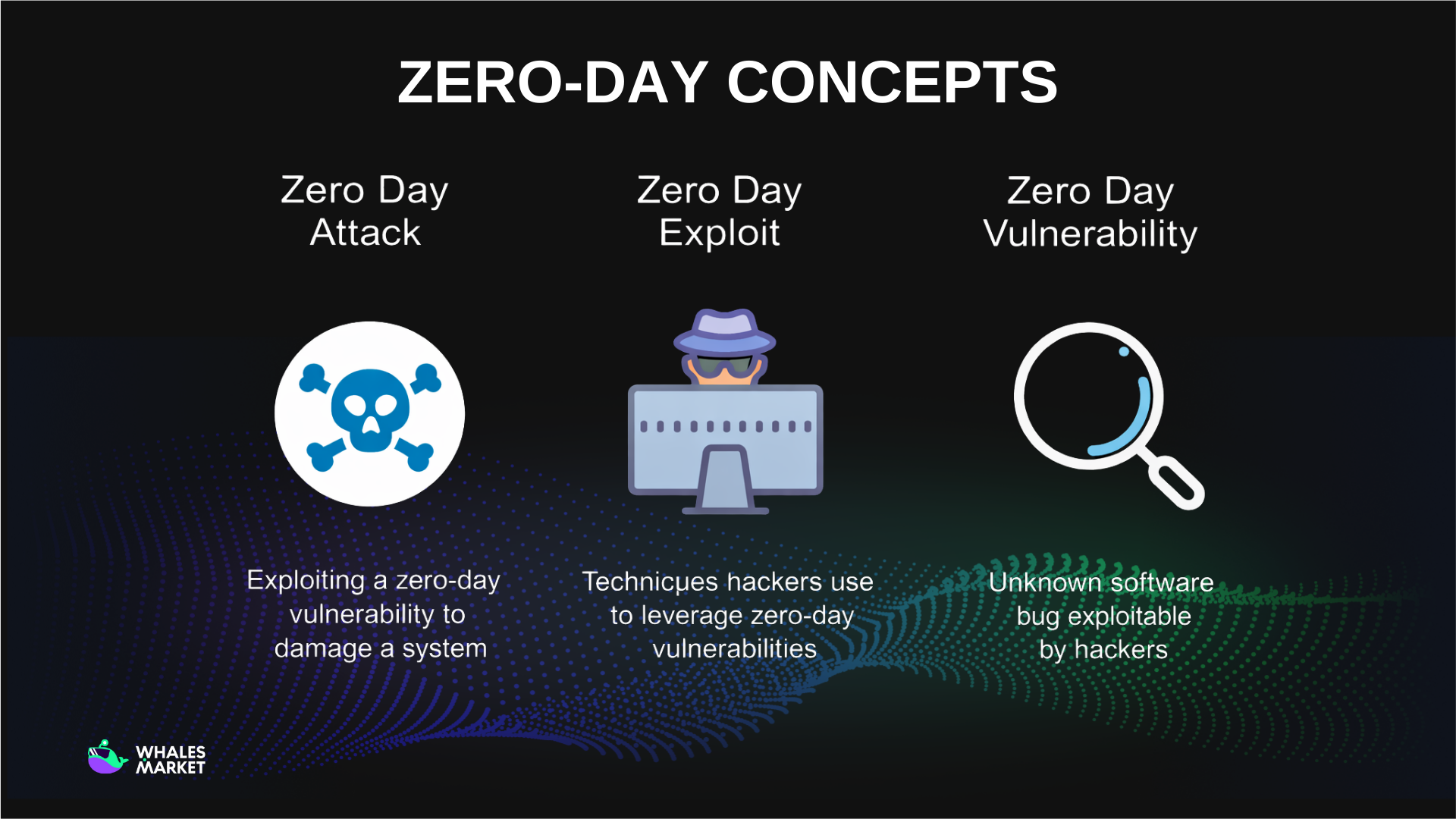
Zero-day Concepts: Attack, Vulnerability & Exploit
Around the concept of zero-day, three closely related terms often appear, each describing a different aspect of the same issue.
- Zero-day vulnerability: These are weaknesses in software discovered by attackers before developers are aware of them. Since the vulnerability has not been identified internally, no patch exists, making it an easy target for exploitation.
- Zero-day exploit: These are the techniques, tools, or code created by attackers to directly take advantage of existing zero-day vulnerabilities.
- Zero-day attack: This is the real-world execution stage, where the exploit is used to cause damage, gain unauthorized access, or steal data from systems containing zero-day vulnerabilities.
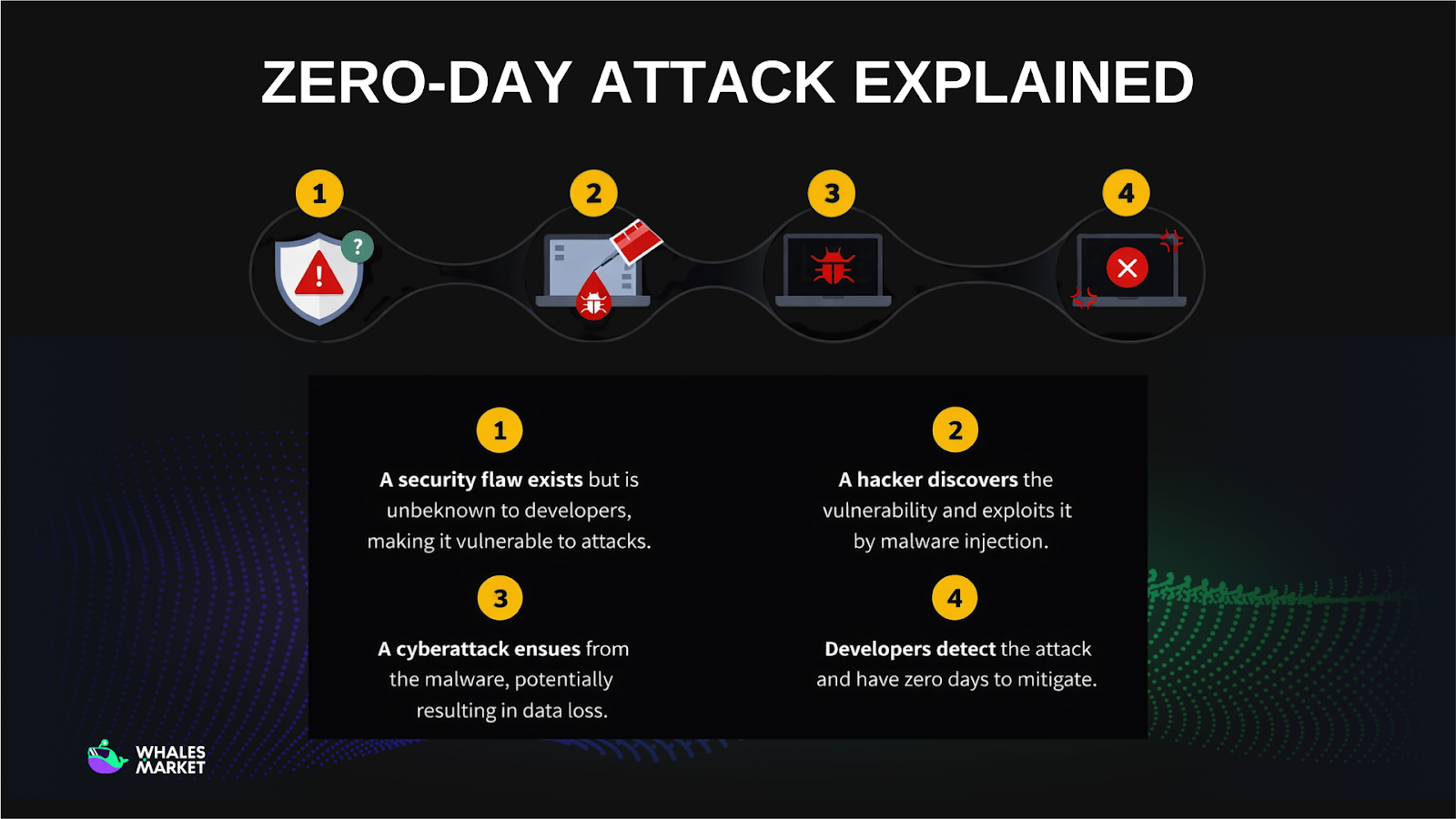
How Does a Zero-Day Attack Happen?
A zero-day attack typically unfolds across four stages.
Stage 1: The vulnerability exists but remains Unknown
The process begins when a security flaw already exists in software, but the development team has not discovered it. Without identification or a patch, the system continues operating normally while remaining silently exposed.
Stage 2: Attackers discover and weaponize the vulnerability
Before developers recognize the issue, attackers identify the flaw and build an exploit to take advantage of it. The exploit can be delivered through malware injection, phishing, social engineering, or by planting malicious code on trusted websites or intermediary software.
Stage 3: The attack executes and causes damage
Once the exploit is triggered, malicious code activates and the attack begins. Attackers may steal data, gain system control, extract private keys, drain wallets, or manipulate transactions. Without a patch, damage often spreads before mitigation becomes possible.
Stage 4: Developers discover the issue with no time to prepare
Only after signs of compromise appear do developers realize the vulnerability exists. At this point, they effectively have “zero-day” to respond, needing to patch systems while actively limiting ongoing damage, often after the exploit has already spread widely.
Difference between Zero-day and One-day attack
These two concepts may sound similar, but their risk levels differ significantly. The key distinction lies in one central question: whether a security patch already exists.
- Zero-day attack exploits a vulnerability that developers are completely unaware of. This means there is no patch, no security advisory, and no specific defensive measure available at the time of exploitation. Attackers have a clear advantage, while victims have virtually no preparation or protection in place.
- One-day attack, also known as an n-day attack, occurs after a vulnerability has been publicly disclosed and a patch has already been released. However, attackers take advantage of the time gap before users or organizations apply the update. In other words, the solution exists, but it has not yet been implemented.
At first glance, one-day attacks may seem less dangerous than zero-day attacks. In reality, they are extremely common and can cause comparable damage. The main reason is simple: many individuals and organizations delay software updates.
Zero-Day Attack Example in Crypto Market
Bybit
This is widely considered the largest crypto hack in history. On 21/02/2025, attackers gained control of the Safe{Wallet} interface, the multi-signature tool Bybit used to manage cold wallets. By injecting malicious JavaScript into the frontend via a Safe developer’s machine, attackers caused Bybit signers to see a legitimate-looking transaction. In reality, they approved a transfer of 401,347 ETH, worth approximately $1.5B, to the attacker’s wallet.
The FBI confirmed that the North Korean Lazarus Group was responsible. According to Chainalysis, the Bybit incident alone exceeded the total amount stolen by North Korean hackers throughout all of 2024. Bybit stated it had sufficient reserves to cover losses, published proof-of-reserves within 3 days, and launched a bounty program offering 10% of recovered assets, roughly $140M.
Bybit’s $1.5B hack is bullish - Lazarus has diamond hands.
— arndxt (@arndxt_xo) February 22, 2025
Led by Park Jin Hyok, now wanted by the FBI.
They’ve just drained $1.46B in staked ETH & ERC-20 tokens from Bybit, making it the biggest crypto hack ever, twice the size of the second-largest breach.
How did they pull… pic.twitter.com/OV1JzWmhYB
Curve Finance
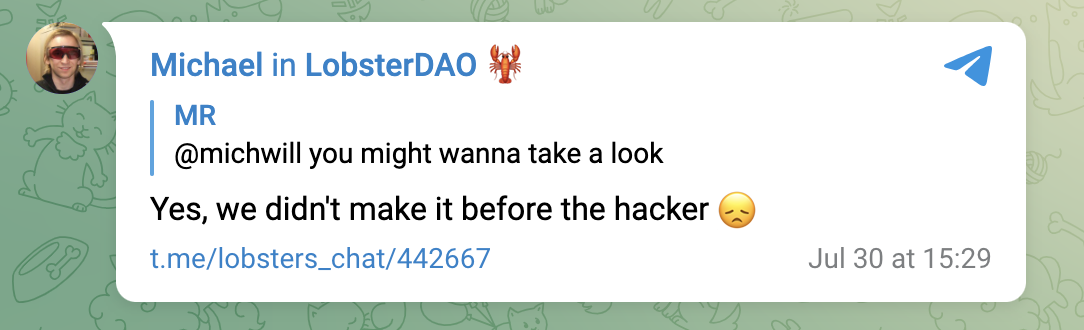
On 30/07/2023, attackers exploited a zero-day vulnerability in the Vyper compiler, specifically versions 0.2.15, 0.2.16, and 0.3.0, a popular language for Ethereum smart contracts. The flaw stemmed from an incorrectly implemented reentrancy lock, allowing attackers to repeatedly call functions and drain funds before balances updated.
Multiple liquidity pools were affected, including Alchemix with $13.6M, JPEG'd $11.4M, Metronome $1.6M, and the CRV/ETH pool at approximately $22M. Initial losses were estimated at $73.5M, but white-hat hackers and MEV bots front-ran transactions to protect funds, reducing actual losses to around $52M.
Notably, Curve Finance TVL fell nearly 50% in a single day, from $3.25B to $1.72B. The CRV token price dropped about 30%, nearly triggering a liquidation cascade on Aave, as Curve’s CEO had a loan close to $100M collateralized with CRV.
How to prevent a Zero day attack
For individual users
- Keep software updated as soon as patches are released: This simple step is often ignored. In many cases, being weeks late is enough to become a victim, as seen when Lazarus exploited Chrome zero-day vulnerabilities before most users updated.
- Use hardware wallets: This is the most important protection layer for large assets. Even if a computer is infected with malware, private keys remain secure on hardware devices, as long as transaction details are carefully verified on the device screen.
- Enable 2FA and avoid password reuse: Authenticator apps such as Google Authenticator or Authy are safer than SMS. Password managers help maintain strong, unique credentials.
- Regularly back up data and store seed phrases offline: Seed phrases should be kept in secure locations, fully isolated from internet-connected devices.
For projects and organizations
- Implement bug bounty programs: These programs incentivize white-hat hackers to find vulnerabilities before malicious actors do.
- Maintain continuous monitoring: On-chain and off-chain monitoring tools help detect anomalies such as unusual transactions, unfamiliar IP access, or unauthorized code changes.
- Apply AI and machine learning for anomaly detection: Modern security solutions analyze behavioral patterns to identify early signals of zero-day attacks.
- Diversify infrastructure dependencies: Relying on a single wallet provider, compiler, or chain increases systemic risk. The Curve Finance incident showed how a compiler flaw can impact hundreds of protocols simultaneously.
Summary
Zero-day attacks represent one of the most serious threats not only in crypto but across the entire technology industry. These incidents are a clear reminder that no system is invulnerable.
With zero-day exploitation accelerating, often within 5 days of disclosure, and AI agents increasingly capable of discovering vulnerabilities autonomously, the race between attackers and defenders will only intensify.
FAQs
Q1. How is a zero-day attack different from typical crypto hacks?
Zero-day attacks exploit undisclosed vulnerabilities with no available patches. This leaves projects and users unable to react in time, often resulting in significantly greater damage than attacks based on known flaws.
Q2. Why do zero-day attacks cause especially large losses in crypto?
Crypto systems rely entirely on software and smart contracts. When a zero-day emerges, attackers can directly target wallets, contracts, or core infrastructure, leading to immediate asset loss and transactions that are difficult to reverse.
Q3. Do zero-day attacks always target smart contracts?
No. Zero-day attacks in crypto can target browsers, wallets, compilers, application frontends, or internal infrastructure. The Bybit and Chrome incidents show that vulnerabilities are not limited to smart contracts.
Q4. Can individual users detect a zero-day attack early?
In most cases, early detection is extremely difficult because exploits operate silently. However, unusual websites, unfamiliar extensions, unclear signing requests, or urgent security updates are signals that require caution.
Q5. Do bug bounty programs really reduce zero-day risk for crypto projects?
Yes. Bug bounties encourage early disclosure by white-hat hackers, allowing teams to patch vulnerabilities before real-world exploitation. Many major incidents have been prevented through these programs.
Q6. Will AI make zero-day attacks more dangerous or safer in crypto?
AI introduces both risk and defense. Attackers can use AI to find vulnerabilities faster, while projects can use AI to detect abnormal behavior and respond earlier to zero-day threats.
Q7. Who was behind the zero-day attack?
Many major cases were linked to organized hacking groups, including North Korea’s Lazarus Group, though attribution often requires lengthy investigations and is not always publicly confirmed.